Imagine trying to verify a single receipt in a warehouse containing millions of boxes. You’d need to open every box, check every label, and cross-reference the entire inventory just to confirm that one item exists. That’s essentially what early digital ledgers struggled with before Merkle trees became the backbone of modern cryptocurrency systems.
A Merkle tree is a hierarchical cryptographic data structure that allows for efficient and secure verification of large datasets. In simple terms, it’s a way of organizing transactions so you can prove a specific piece of data belongs to a larger set without needing to download or process the entire set. This isn’t just a nice-to-have feature; it’s what makes decentralized networks like Bitcoin and Ethereum actually usable on everyday devices.
How Merkle Trees Actually Work
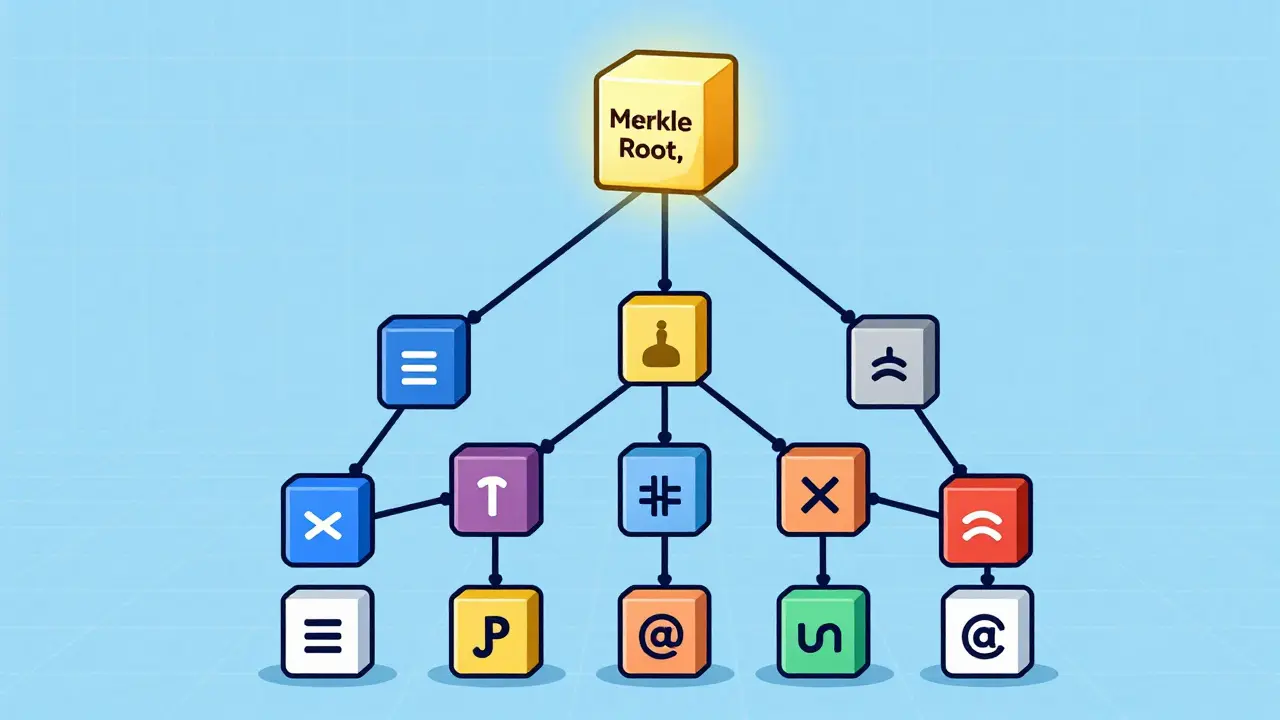
To understand why Merkle trees are so powerful, you first need to see how they’re built. Think of them like an upside-down family tree. At the bottom, you have your "leaf nodes." In a blockchain context, these leaves are individual transactions.
Here’s the step-by-step process:
- Hashing the Leaves: Each transaction is run through a cryptographic hash function (like SHA-256 in Bitcoin). This turns the transaction data into a unique string of characters called a hash.
- Pairing Up: These leaf hashes are paired up. Two hashes are combined and hashed together again to create a parent node.
- Repeating the Process: This pairing and hashing continues upward, layer by layer, until only one hash remains at the very top.
- The Merkle Root: This final hash is the Merkle root. It sits in the block header and acts as a digital fingerprint for every single transaction in that block.
The magic lies in the math. If you change even a single comma in one transaction at the bottom, the hash changes completely. That new hash propagates up the tree, changing every parent hash along the way, ultimately resulting in a totally different Merkle root. This makes the structure incredibly sensitive to tampering while remaining compact.
Efficient Transaction Verification for Light Clients
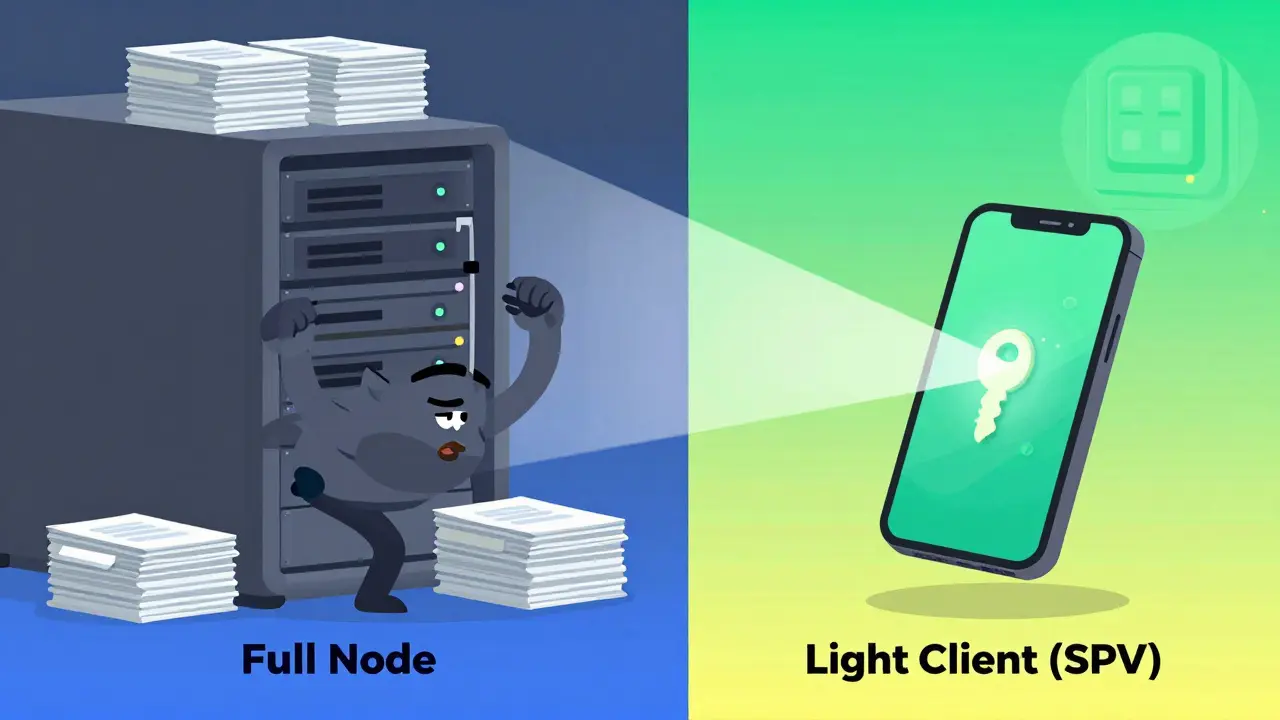
One of the biggest hurdles in blockchain technology is scalability. Full nodes-computers that store the entire history of the blockchain-are heavy. They require terabytes of storage and significant bandwidth. Not everyone has a server farm in their basement. Most of us use smartphones or laptops.
This is where Simple Payment Verification (SPV) comes in. SPV relies entirely on Merkle trees. Instead of downloading the whole block to check if you received payment, your wallet requests a "Merkle proof."
A Merkle proof is just a small path of hashes from your specific transaction up to the Merkle root. It includes your transaction’s hash, its sibling’s hash, and the siblings of those parents all the way to the top. With this tiny amount of data, your device can mathematically prove that your transaction is included in the block represented by the Merkle root stored in the block header.
You don’t need to trust anyone else. You don’t need the full ledger. You just need the root and the proof. This allows mobile wallets to operate securely and quickly, verifying transactions in seconds rather than hours.
| Feature | Full Node | Light Client (SPV) |
|---|---|---|
| Data Required | Entire blockchain history | Block headers + Merkle proofs |
| Storage Needs | High (Terabytes) | Low (Megabytes/Gigabytes) |
| Verification Speed | Slower (initial sync) | Near-instant |
| Trust Model | Self-sovereign | Cryptographically verified |
Unbreakable Data Integrity and Tamper Detection
In a system where money moves digitally, integrity is everything. If someone could alter a transaction record after the fact-say, changing the recipient address or the amount-the entire trust model collapses. Merkle trees make this practically impossible.
Because the Merkle root is embedded in the block header, and that header is linked to the previous block via its own hash, any attempt to modify a past transaction creates a chain reaction. The attacker would need to recalculate the Merkle root for that block, then the hash of that block, then the Merkle root of the next block, and so on, all the way to the present day. They would also need to do this faster than the rest of the network combined.
This property is known as collision resistance. It means it is computationally infeasible for two different sets of transactions to produce the same Merkle root. If a malicious actor tries to inject a fake transaction or alter an existing one, the resulting Merkle root will not match the one recorded in the block header. Nodes across the network will immediately reject the block as invalid.
This provides a robust mechanism for tamper detection. You don’t need to inspect every byte of data to know it’s been compromised. A mismatch in the root hash is immediate proof of foul play.
Massive Gains in Storage and Bandwidth
Blockchain networks are inherently inefficient because every participant stores a copy of the data. Without optimization, this inefficiency would grow exponentially as transaction volumes increase. Merkle trees act as a compression algorithm for verification purposes.
Consider the difference in data size. A typical Bitcoin block might contain thousands of transactions, totaling several megabytes of raw data. However, the Merkle root is just 32 bytes (256 bits). By storing only the root in the block header, the network reduces the overhead associated with linking blocks together.
When syncing a new node, the network doesn’t need to transfer every single transaction immediately. It can transfer block headers and Merkle roots first. This allows for rapid synchronization of the blockchain’s structure. Detailed transaction data can be fetched on demand using Merkle proofs. This drastically reduces the bandwidth required for network communication, keeping transaction fees lower and confirmation times faster.
Enhancing Privacy Through Selective Disclosure
While public blockchains are transparent, users still want privacy. They don’t want strangers scanning their entire transaction history. Merkle trees enable a balance between transparency and privacy through selective disclosure.
Protocols like zk-SNARKs (Zero-Knowledge Succinct Non-Interactive Arguments of Knowledge) often utilize Merkle tree structures to prove ownership or validity without revealing the underlying data. For example, you can prove you have enough funds in a specific account without revealing your total balance or the other transactions in that account. The Merkle proof shows your transaction is part of the valid state tree, but nothing else.
This is crucial for scaling solutions like Layer 2 networks (e.g., Lightning Network or Rollups). These systems process thousands of transactions off-chain and then submit a single Merkle root to the main blockchain. The main chain verifies the root, trusting that all the complex interactions happened correctly based on the cryptographic guarantee, without clogging the main ledger with every minor detail.
Real-World Applications Beyond Bitcoin
While Bitcoin popularized Merkle trees, their utility extends far beyond simple peer-to-peer cash. Here’s how they’re used in broader crypto ecosystems:
- Ethereum State Management: Ethereum uses a variant called the Merkle Patricia Trie to store the current state of accounts (balances, contract code, storage). This allows the network to efficiently update and verify the state of millions of users without rewriting the entire database.
- File Storage Networks: Projects like IPFS (InterPlanetary File System) use Merkle DAGs (Directed Acyclic Graphs) to ensure file integrity. When you download a file, the system checks the Merkle root to ensure no bits were corrupted during transfer.
- Cross-Chain Bridges: When moving assets between different blockchains, bridges use Merkle proofs to verify that a transaction occurred on Chain A before releasing tokens on Chain B. This prevents double-spending across ecosystems.
Limitations and Challenges
No technology is perfect. Merkle trees have some inherent limitations that developers must work around:
- Tree Depth: As blocks get larger, the tree gets deeper. A deeper tree means longer Merkle proofs, which increases the data load for light clients. Developers optimize this by using balanced trees or alternative structures like Hashing Keccak trees.
- Second Preimage Attacks: While rare, theoretical vulnerabilities exist where two different inputs could produce similar hashes under specific conditions. This is why choosing strong, well-vetted hash functions (like SHA-256 or Keccak-256) is critical.
- Computation Overhead: Calculating hashes requires CPU power. For extremely high-throughput systems, the cost of generating the tree can become a bottleneck, though this is rarely an issue compared to the benefits gained.
The Future of Merkle Trees in Crypto
As blockchain technology evolves, Merkle trees remain fundamental. New innovations like Verkle Trees are emerging to replace traditional Merkle trees. Verkle trees combine Merkle trees with vector commitments, allowing for even smaller proofs and better privacy. They aim to reduce the size of state data further, enabling true "stateless" clients who don’t need to store any historical data at all.
The shift toward modular blockchains, where execution, consensus, and data availability are separated, relies heavily on Merkle-based proofs to ensure interoperability. Whether you’re building a DeFi app, a NFT marketplace, or a private enterprise ledger, understanding how Merkle trees secure and scale your data is essential.
They turn the impossible task of verifying millions of records into a simple mathematical check. That’s not just efficiency; that’s the foundation of trust in a trustless world.
What is a Merkle tree in simple terms?
A Merkle tree is a data structure that organizes information into a tree-like format where each leaf node contains a hash of data (like a transaction), and each parent node contains the hash of its children. This continues until a single "root" hash represents the entire dataset. It allows you to verify if a specific piece of data is part of the whole without needing to download the entire dataset.
Why are Merkle trees important for Bitcoin?
Merkle trees are crucial for Bitcoin because they enable Simple Payment Verification (SPV). This allows lightweight wallets (like those on phones) to verify transactions without downloading the entire blockchain. They also ensure data integrity by making it nearly impossible to alter past transactions without detection, securing the network against tampering.
How does a Merkle proof work?
A Merkle proof is a small subset of hashes from the Merkle tree that connects a specific transaction to the Merkle root. To verify a transaction, you take the transaction's hash, combine it with the provided sibling hashes step-by-step up the tree, and check if the final result matches the Merkle root stored in the block header. If it matches, the transaction is valid and included in the block.
Can Merkle trees be hacked?
Merkle trees themselves are mathematically secure, relying on cryptographic hash functions like SHA-256. While the structure is robust, potential weaknesses lie in the implementation or the choice of hash function. However, breaking a Merkle tree would require finding a collision (two different inputs producing the same hash), which is currently computationally infeasible with existing technology.
What is the difference between a Merkle tree and a Merkle Patricia Trie?
A standard Merkle tree is a binary tree used primarily for ordering transactions within a block. A Merkle Patricia Trie is a more complex data structure used by Ethereum to store key-value pairs (like account balances). It combines features of a Merkle tree, a Patricia trie (for efficient searching), and allows for dynamic updates to the state without rebuilding the entire tree.
Do Merkle trees save storage space?
Yes, significantly. Instead of storing the full details of every transaction in the block header, only the 32-byte Merkle root is stored. This compresses the representation of thousands of transactions into a tiny fixed-size value, reducing the overhead for block propagation and synchronization across the network.
What are Verkle trees and how do they improve on Merkle trees?
Verkle trees are a newer evolution that replaces hashes with polynomial commitments. This allows for much smaller proofs and enables "stateless" clients, which can verify transactions without storing any historical state data. They offer better privacy and scalability compared to traditional Merkle trees, particularly for large-scale blockchain states.